SSH (Secured SHell) is a secure cryptographic network protocol for operating systems to let remotely access your hosting. It is used for managing networks, operating systems, and configurations. It is also inside many file transfer tools and configuration management tools. Most of the top corporation use SSH in almost every data centre. The modern web and computerised services are made cost-effective with the automation provided by SSH keys. This makes things more convenient and highly secured while handling. So, here is the blog about configuring SSH keys for multiple accounts in Github.
Benefits of SSH keys
- Highly secured alternative username/password authorization.
- Being generated in public/private keys, SSH keys lets you share your public key with others and the private key is available on the machine only.
- You can access your GitHub through SSH by sharing your public key.
Who Has Multiple SSH Keys?
One can say that almost every developer browsing around the web sphere have witnessed or encountered SSH in any way. SSH is used for connecting with remote servers that incorporated managing code with the help of GIT and by syncing it with remote repositories. You might be using one SSH key-pair for working on your company’s internal projects but you might be using a different key for accessing some client’s company projects in the same git account. In some cases, there are even possibilities of using different keys to access your own private server.
ALSO READ:Top 10 Best Tech Companies For Employees To Work In The USA In 2020
It helps to manage multiple SSH keys for different GitHub, GitLab accounts so that you can access multiple accounts and projects, each with different credentials.
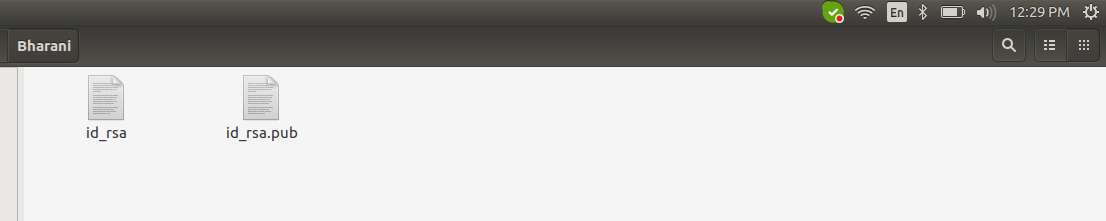
Create a folder inside .ssh folder in a new name[ eg. New ] and paste ssh key files inside the folder.
Create a config file inside the .ssh folder and update it with the below content. Self git accounts for your own SSH key and new for newly included one, differentiate with help of Host.
# Self git account Host github.com HostName github.com User git IdentityFile ~/.ssh/id_rsa # New git account Host github.com-New HostName github.com User git IdentityFile ~/.ssh/New/id_rsa
Adding an Arbitrary Key
The first and foremost thing to do when adding an arbitrary key is to give the path of the key file as an argument to ssh-add. See the code snippet below.
ssh-add ~/.ssh/New/id_rsa
List ssh keys
You can make use of the -l option to ssh-add in order to list them by fingerprint. Follow the code snippet shown here.
ssh-add -l
ALSO READ: How To Convert Your WordPress Site into a PWA
Add a New Remote to Your Git Repo
If you want to add a new remote to your Git Repo, you should use git remote add command on the terminal in the directory where your repository is stored. You need to know how to use the git remote add command. It takes two arguments as shown below. A remote name, here it is “origin” and a remote URL which is present on the source sub-tab of the Git repo.
git remote add origin git@github.com-New:projectname.git
Pull Git Repository
When you are running the git pull command, it actually runs git fetch. This git fetch downloads all the content from the remote repository that is specified. Moreover, git merge gets executed to merge the remote content refs. This results in a new local merge commit.
git pull origin master
Clone Git Repository
git clone git@github.com-New:projectname.git
Challenges
Why do you get an unprotected private key file error?
@ WARNING: UNPROTECTED PRIVATE KEY FILE! @ @@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@ Permissions 0777 for '/home/path_to_id_rsa are too open. It is required that your private key files are NOT accessible by others. This private key will be ignored.
It is important for you to understand that the “Permission denied (public key)” is from the remote server. So, you might be using the wrong key which is not allowed to connect. Or else, there must be a typo in the remote authorized_keys file.
How to fix the unprotected private key file error?
Using this command, fix the issue.
chmod 400 /home/path_to_id_rsa ssh-add ~/.ssh/path_to_id_rsa
This message appears in the terminal.
Identity added: /home/new_path_to_id_rsa (/home/path_to_id_rsa)
Set Up config keys
Checkout to your working directory and check the config details using the command. If config keys are based on the self account, update it with a new username and email for the corresponding ssh.
ALSO READ: Top 10 IT Staffing and Recruiting Agencies in USA
Note: Don’t use –global
git config –list git config user.name "user_name" git config user.email "email@gmail.com"
Check the config file
After update check this command for whether the credentials are created or not to the corresponding repository.
nano .git/config
Conclusion
The above commands should cover the majority of the information most developers will need about SSH on a day-to-day basis. Remember to keep your private keys safe. You can configure the same ssh key in multiple systems if you wish, or generate new ones on each client connecting to your web server for added security. Each user should generate their own SSH key pair for secure access control. With proper management, Multiple users can configure the same ssh keys for convenience.
If you have a business idea in your mind and searching for a reliable web development company, you are in the right place. Hire the best web developers in the industry from Agira technologies.







